TrickBot is once again making itself known during tax season and attempting to steal your hard-earned money. TrickBot was originally discovered in October of 2016 but has since changed and evolved dramatically into one of the most prolific hacking attacks today.
How it works
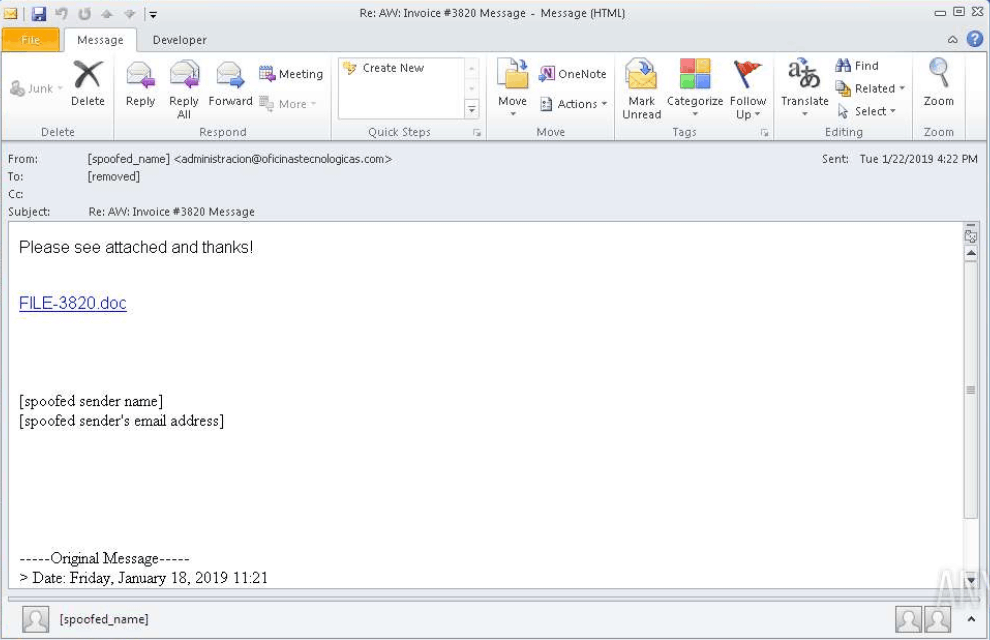
Just like Emotet, TrickBot primary spreads by specially designed emails or malspam that attempts to trick the user into clicking or downloading the attachment. The current campaign, as of this writing, is TrickBot’s normal tax season attack: pretending to be the IRS. In the example below, the link will send you a to a domain that looks official but is slightly misspelled.
Once TrickBot is installed on a computer, it sets up a scheduled task to make sure it has a persistent presence on the computer before starting to steal information. In addition, it disables Windows Defender early on so that it won’t be removed. SUPERAntiSpyware is not stopped in this way.
TrickBot does not show any signs of running on a user’s
computer and the only “noise” it makes is the network traffic it creates.
Recording network traffic is generally only done by businesses, which helps
TrickBot evade detection on personal computers.
TrickBot uses a module design, much like Emotet and other bankers. Not only does this allow TrickBot to quickly
change its attack capabilities, but it also makes it harder to detect. These
modules often do one thing well rather than trying to do many things. Some are
designed to go after hosted ftp servers, cached remote desktop credentials, and
bitcoin mining accounts.
The most common module, however, allows TrickBot to redirect the user to fake bank sites that, instead of logging the user in, will steal account credentials. The scammers make this possible by domain squatting, or registering an internet address that is only slightly different than the one you intend to visit. For instance, if you receive an email about your GoDaddy account, you might not notice if a link in that email goes to godabdy.com/payyourbill (godaddy is misspelled with a b instead of the second d).
This is compounded upon by hiding the URL so only the studious will look for it and by making the site look like you expect through careful recreation by the attackers. Many big companies will attempt to combat this by buying these fake sites and then redirecting them to the appropriate domain, but this is not always easily done.
Who is affected?
TrickBot is aimed more at business than casual users; however, it is still the number-one banker, and anyone who lives inside the USA, Africa, Europe, and Middle East should be wary. (This does not exclude other areas from being hit, just shows that they are not the current target.)
Indicators of Compromise
- C:\Documents and Settings\<USER>\Application Data\Microsoft\Crypto\RSA\S-1-5-21-1275210071-920026266-1060284298-1003\8c8436195f6e0875edb85e34665c32ec_fabbc6a1-c573-4ea0-9ca1-50004b35a440
- C:\d2cc298a90c6ef939488b53ead12fd3549c3c0414733f6fdaf1762da31ea1e90
- sha256: d2cc298a90c6ef939488b53ead12fd3549c3c0414733f6fdaf1762da31ea1e90
- sha1: df404c6b1efc2cfbfdd0b7699554989dab03791f
- md5: e580ca34929cf9b62e816adcebe715f2
- C:\Users\admin\AppData\Roaming\msscsc\e690ca34929cf9b72e917adcebe816f2.exe
- d2cc298a90c6ef939488b53ead12fd3549c3c0414733f6fdaf1762da31ea1e90
- http://ip.anysrc.net/plain/clientip
- Scheduled Task that points to a file in AppData such as C:\Users\<User>\AppData\Roaming\
What you can do
If you or someone you know is infected with TrickBot malware, download SUPERAntiSpyware Professional right now and get a 14 day free trial, no credit card required. SUPERAntiSpyware is easy to install and will detect and remove TrickBot from any Windows computer. If you are a Computer Technician, you may like to try our SUPERAntiSpyware Tech Edition solution, now free for the next 30 days. Use Tech04 as the Tech ID. Click here: https://www.superantispyware.com/technician-download.html

Thanks for the really valuable tip. SUPERAntiSpyware Professional is really powerful to fight TrickBot. Will recommend this program to my colleges.
This is great, I have been looking for some quality anti spyware. Going to be doing some more research into this one, thanks!