The internet today is just as dangerous of a place as it ever was. Sure, there are plenty of trusted websites you visit on a daily basis that pose little to no risk to your computer. The worst that happens to most people are unwanted tracking cookies from ad servers being placed on their machine, which is a small price to pay for free access to these sites, especially since they are so easy to remove with programs such as SUPERAntiSpyware®.
Today we’re going to talk about Potentially Unwanted Programs or PUPs for short.
What are PUPs?
PUPs live in the grey area of the software spectrum. Sometimes, they can provide a service that you want, such as coupons or the ability to download videos from popular sites like YouTube; however, sometimes the programs that we classify as PUPs can be the underlying cause of unwanted behavior, such as displaying ads, installing other pieces of software, or modifying your web browser’s homepage.
The most common sources of PUP “infections” are download websites that bundle other pieces of software in with the software that you are really trying to get. Unfortunately, many of the companies that make legitimate software don’t have a say in this bundling of software, as the download host is the one that is making a special installer that will offer up these other pieces of software before you can, or in order to, download and install the piece of software you want.
Many people just click the next button over and over again until they get the software they want installed. The downside to this method of installing software is that you leave yourself susceptible to PUPs on your machine, oftentimes not realizing what has been installed until it is too late. This is what many of these bundled installers are hoping for. They want you to blindly click through so they can get paid for the install of software, as these sites get paid for each piece of software they are able to distribute to end-users, even if they don’t necessarily want what they’re getting.
Once a computer has been “infected” by a PUP, the user may notice some major performance slowdowns or other erratic behaviors. The most common side-effects of PUPs include unwanted or unknown software popping up on your screen telling you there’s a problem, advertisements taking over your screen (either through the web browser directly, or through pop-ups outside the main browser window, system resources being hogged (slowing down the computer), toolbars being installed without your knowledge, and your browser’s homepage being redirected to an unknown/unwanted website.
How can I protect myself from PUPs?
The easiest way to avoid installing PUPs is to make sure that you’re downloading programs from trusted sources (always from the software publisher, if possible), you’re reading each of the screens on install wizards (removing any unwanted options from the installation), and do your research on whether or not the software that you’re looking for is safe and held in high regard by members of the community.
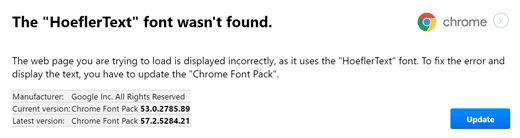
One of the biggest traps that are out there in the wild is the ubiquitous “Big Button”. You have probably seen these before. Say, for example, you’re looking for new media player software to play movies and music. In order to get that software, you go to a file hosting website, and you’re immediately greeted with three green buttons, a red button, and a yellow button, all with the word “DOWNLOAD” in bold capital letters across the center of it. Which one is the correct button to press?
Sometimes reading through the website isn’t enough to show you exactly which button is the real button, and which is an advertisement for another piece of software that’s been embedded near the correct button. Some websites even offer two different versions of the software: one that’s a clean installer, the other is an ad-supported/bundled installer.
This is why we recommend trying to download the software you want directly from the company who makes it. They want you to use their software, so they’re going to make it as easy for you as possible to get what you want. That means no bundled software and no ads that are disguised as download links.
Keep in mind that not all bundled software is bad. Many programs will offer downloads of legitimate products, such as Google Chrome or Dropbox. It’s a common occurrence in the software industry; however, if you’re not familiar with the name of the product a company wants you to install, you should always err on the side of caution and opt out of having that software installed.
How do I get rid of PUPs?
Most PUPs can be removed by going into your control panel and uninstalling them just as you would any other piece of software. In some cases, this unfortunately doesn’t always work. Programs such as SUPERAntiSpyware® try to remove these PUPs before scans, and most of the time we’re successful; however, new PUPs, new malware/spyware threats, and variants of existing threats, are created daily.
A couple easy ways to try to get rid of these PUPs before running more in-depth cleaning are to make sure you remove any unknown browser extensions in your web browser, and using the add/remove programs feature within Windows. Typically these PUPs will have their own uninstall files that can easily remove the threat once it is known. As always, make sure you exercise caution when removing programs, as not all “unknown” programs are malicious.
If you think that your machine might have PUPs that you can’t seem to get rid of, or any other malware infection for that matter, the best course of action is to first figure out exactly what you’re dealing with. If there is any distinguishing information you can see (like the program name), do a quick search to see how to remove the program. Most of the time, there will already be a removal guide available for the specific PUP or threat you’re dealing with.
Dealing with pesky PUPs can be time consuming, but remember, the time you take to fix the issue when you first notice it is time you save dealing with a computer that’s been slowed down by these unnecessary and unwanted programs.
Why are you calling <Software Name> a PUP? There’s nothing wrong with it!
There are many different criteria that go into classifying a piece of software a PUP. Keep in mind that the first letter of the acronym stands for POTENTIALLY. If a piece of software you want or use on a regular basis is being detected as a PUP, you’re more than welcome to keep using it or ignore the detection within SUPERAntiSpyware®.
We try to not remove anything from your machine unless we know that it has un-welcomed side effects. Some of the criteria we use for determining if a piece of software is a PUP is outlined below:
– The software is known to display advertisements. This covers everything from pop-ups, pup-unders, ad overlays, inserting in-text ads, and replacing existing advertising streams.
– Hijacking one or more installed web browser. This covers everything from redirecting the homepage (with or without permission), altering search results, inserting bookmarks, installing unwanted add-ons/extensions, and installing toolbars that bring value to the maker rather than the user.
– Bundling other software. This covers everything from including other software as a bundle (optional or otherwise) with a desired piece of software, being included in a bundle from another software or download site, making it difficult/impossible to opt-out of bundled software.
– The overall sentiment of the program is bad. This covers install and uninstall trends for particular pieces of software based on reviews and removal guides from trusted sources, using alarmist notifications to trick the user into purchasing, forcing a purchase to clean or fix issues with or without explaining what the issues are, and using misleading uninstallers to either force download more undesirable software or trick users into keeping the software.
While this is by no means a comprehensive list, it is definitely a good starting point as to why we consider a program as being undesirable. There are plenty of other software review websites out there that will probably echo our sentiments; however, as always, if something is working for you, feel free to ignore the detection.





.png)